Every healthcare provider in the country must abide by strict Health Insurance Portability and Accountability Act (HIPAA) regulations. The Act became law in 1996, aiming to simplify healthcare, prevent fraud, and increase efficiency. The list of HIPAA regulations is long, with many opportunities for mistakes and violations. Learn the most common reasons for compliance breaches to keep your establishment on the right side of the law.
Loss or Theft of Unencrypted Devices
One of the most common HIPAA violations that healthcare organizations face involves the loss or theft of unencrypted devices. These devices: laptops, smartphones, USB drives, and external hard drives.
Often contain protected health information (PHI). If not properly secured, they can become a conduit for unauthorized access, leading to a major HIPAA violation.
The loss or theft of unencrypted devices often happens due to the mobility and small size of these devices.
This vulnerability highlights the need for healthcare organizations to implement strict security measures. These measures include encrypting all devices that store or transmit PHI. Encryption converts the information into a code that can only be deciphered with a specific key, making it unreadable to unauthorized individuals. Even if a device is lost or stolen, encryption will protect the PHI stored on the device.
In addition to encryption, healthcare providers should have strict policies for the use and storage of mobile devices. Staff should be educated about the importance of protecting these devices and the potential ramifications of a HIPAA violation. This could include training on secure password practices, recognizing phishing attempts, and appropriate responses if a device is lost or stolen.
It’s also beneficial to implement a mechanism to remotely wipe data from devices in case they are lost or stolen. This adds an extra layer of security, ensuring that even if a device falls into the wrong hands, the data it holds can be erased before it can be accessed.
Unauthorized Accessing of Protected Health Information
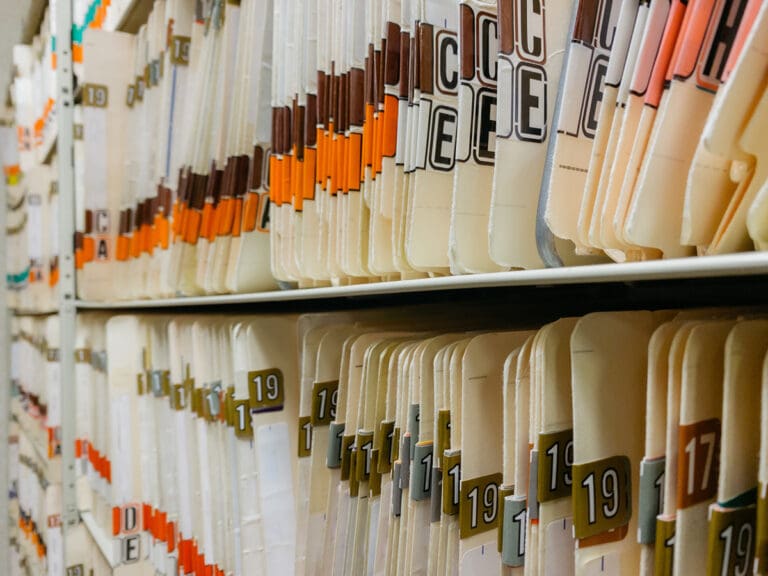
Errors dealing with protected health information (PHI) are the most common HIPAA violations. The rules for storing, accessing, and disposing of sensitive medical records and personal information are strict. It can be easy to violate a rule and expose patient records to data breaches. Unauthorized access to PHI can occur if the hospital fails to store the medical records in a secure facility.
Storing PHI and other sensitive information in a safe off-site records facility can help healthcare establishments save room, resources, and money while guaranteeing secure, breach-free storage. Organizations in the healthcare industry should invest in suitable document storage to prevent unauthorized individuals from gaining access to sensitive information; otherwise, they could face lawsuits.
When a healthcare establishment discovers there has been unauthorized access of PHI, the HIPAA Breach Notification Rule spells out specific steps that must be taken. All affected patients must be notified. The healthcare provider must tell the Department of Health and Human Services about the breach, and in some cases, the media must be notified as well. These notifications must take place in a timely manner, specified in the HIPAA rules.
Failure to Manage PHI Risks and Implement Safeguards
HIPAA mandates that all “covered entities,” such as hospitals and physicians, take responsibility for all aspects related to PHI. This includes managing common risks by conducting risks analyses, keeping PHI confidential, and making PHI available to patients and providers. To achieve all the requirements under HIPAA, healthcare facilities should consider working with an experienced third-party document storage provider.
Outsourcing PHI document management solutions can be the answer to complying with stringent HIPAA regulations while still accommodating patients and others in the medical industry. HIPAA-compliant medical records storage can keep sensitive data secure and free from prying eyes. The right provider can also take care of PHI data encryption, physical access control, secure records transmission, employee training, and more.
Improper Disposal of Protected Health Information
Disposing of PHI once the facility has entered information into a database or no longer has a use for it also comes with strict HIPAA rules. The law states that covered entities must apply appropriate safeguards (physical, administrative, and technical) to address the final disposition of electronic and physical media. Healthcare facilities are responsible for implementing processes for removing PHI data safely and securely. Improper disposal is a serious violation with stiff penalties.
Covered entities under HIPAA cannot simply dump PHI or abandon it somewhere; yet the rules do not detail a specific disposal method. Instead, it is up to the covered entity to come up with their own way of disposing of PHI in a way that will protect the information. Partnering with a trusted third party for secure document destruction can be an easy and stress-free way to handle protected health information without privacy breaches or patient rights violations. Trusting professionals who specialize in the destruction of PHI can ensure HIPAA compliance.
Armstrong Archives, LLC, can make sure you remain compliant. We supply HIPAA-compliant document storage, disposal, and more. Contact us today for more information.

Posted By: Sherri Taylor – President/Managing Partner
Sherri Taylor is the Managing Partner and President of Armstrong Archives, one of the largest independent records and information management companies in the Dallas/Ft Worth area.